End of implicit internet access for new Azure VNets
- Maxime Hiez
- Azure
- 24 Mar, 2026
Introduction
Starting March 31, 2026, Microsoft is making a major change to Azure’s default network behavior. New Virtual Networks (VNet) will no longer have implicit outbound internet access. All internet connectivity will now need to be explicitly configured, for example, via an Azure NAT Gateway, a firewall, or a load balancer with outbound rules. This change marks the end of a long-standing, often overlooked, but widely used Azure behavior.
How did Azure work until now ?
Historically, when a virtual machine was deployed in a VNet without a public IP address, without a NAT Gateway, and without an explicit outbound rule, Azure still provided automatic outbound internet access. This mechanism is called Default Outbound Access (DOA) :
- Azure assigned a Microsoft-managed public IP address in the background
- This IP address could change without notice
- Outbound traffic was largely invisible, difficult to control, and unauditable
What exactly changes
Starting March 31, 2026 :
- All new VNets created in Azure will be private by default
- Subnets will have the property defaultOutboundAccess = false
- No outbound internet access will be available without explicit configuration
In practice, a VM deployed in a new VNet will no longer have internet access by default and will need to use an explicit solution :
- Azure NAT Gateway (recommended)
- Azure Firewall / third-party firewall (Fortinet, Checkpoint, etc.)
- Load balancer with egress rules
- Public IP address (not recommended in production)
note
Why is Microsoft making this change ?
Microsoft justifies this decision with several strategic objectives :
Security
Implicit internet access goes against the Zero Trust principles. A resource should never have external connectivity without an explicit decision.
Governance and auditing
-
Implicit outgoing IPs :
- Do not belong to you
- Can change
- Are difficult to trace
-
With a NAT Gateway or firewall :
- IPs are static
- Traffic is logged
- Flows are predictable and controlled
Who is actually impacted ?
No impact for :
- Existing VNets (created before March 31, 2026)
- VMs already in production
- New VMs deployed in existing VNets
Direct impact for :
- Any new VNet created after March 31, 2026
- Development / test environments created “on the fly”
- Automated deployments that assume implicit internet access
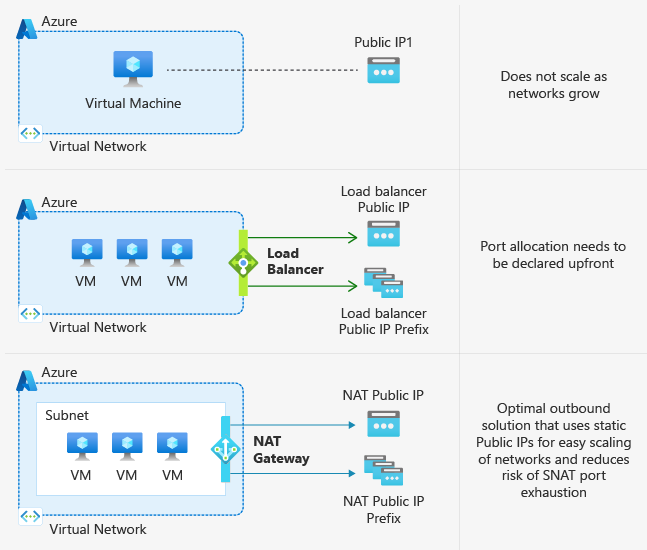
Azure NAT Gateway : The preferred solution
Microsoft clearly recommends Azure NAT Gateway as the default method for restoring outbound connectivity, with key advantages including :
- Static public IP address (or IP prefix)
- Automatic SNAT port management
- Built-in high availability
- Simplified deployment (subnet association)
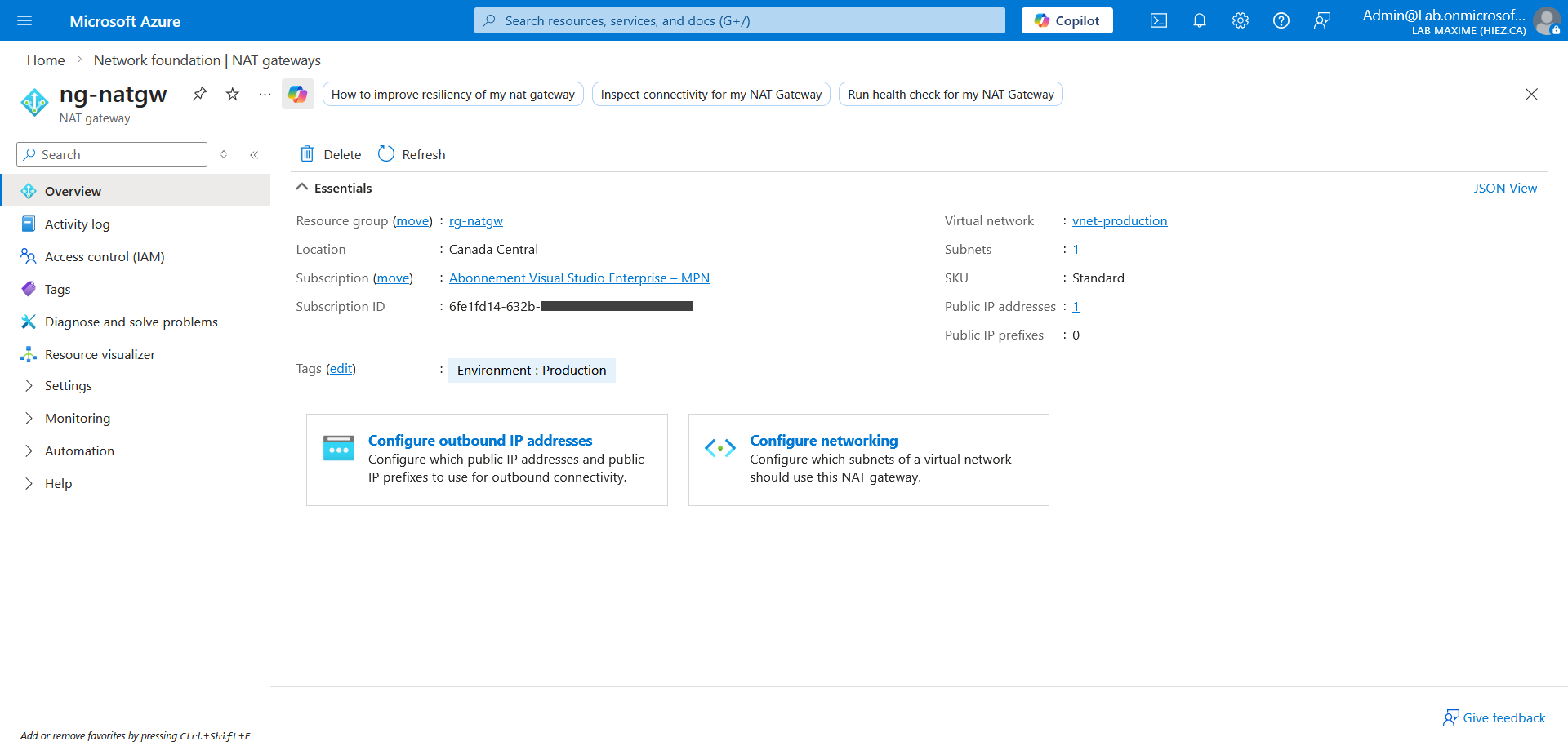
Today, this is the simplest and cleanest option to replace Default Outbound Access, especially for SMEs and environments without a central firewall.
How much does Azure NAT Gateway cost ?
Billing starts when the resource is created. Data processing charges for NAT Gateway include outbound and return data.
Azure NAT Gateway offers 2 SKUs, Standard and StandardV2. Standard provides single availability zone support, whereas StandardV2 provides zone redundancy. Both are matched in price. There is no cost difference between the two SKUs.
- Resource hours : 0,06158$ per hour
- Data processed : 0,06158$ per GB
Conclusion
The change introduced by Microsoft on March 31, 2026, marks a significant milestone in the evolution of Azure’s network model. By ending implicit outbound internet access for new Virtual Networks, Azure is definitively abandoning a “it just works” approach in favor of a secure, explicit, and controlled one.
While this change won’t disrupt existing environments, it does impose a new design discipline for all future deployments. From now on, all outbound connectivity must be intentionally planned, documented, and configured.
Beyond the technical constraints, this is primarily an opportunity to regain control over network traffic, improve governance, strengthen security, and finally align Azure architectures with the principles of secure by default and Zero Trust.
Sources
Microsoft Learn - Default outbound access in Azure
Microsoft Learn - Azure NAT Gateway
Microsoft - Azure NAT Gateway pricing
Did you enjoy this post ? If you have any questions, comments or suggestions, please feel free to send me a message from the contact form.
Don’t forget to follow us and share this post.